
Indian education sector most targeted by cybercriminals globally in July 2021: Check Point


Tel Aviv, Israel-based IT security solutions provider Check Point’s research wing has revealed in a study that in July 2021, there was a 29% increase in attacks against organizations in the education sector compared to the first half of 2021. What is concerning is that Check Point Research (CPR) showed that country-wise, education organizations in India were most targeted, followed by Italy and Israel.
.jpg)
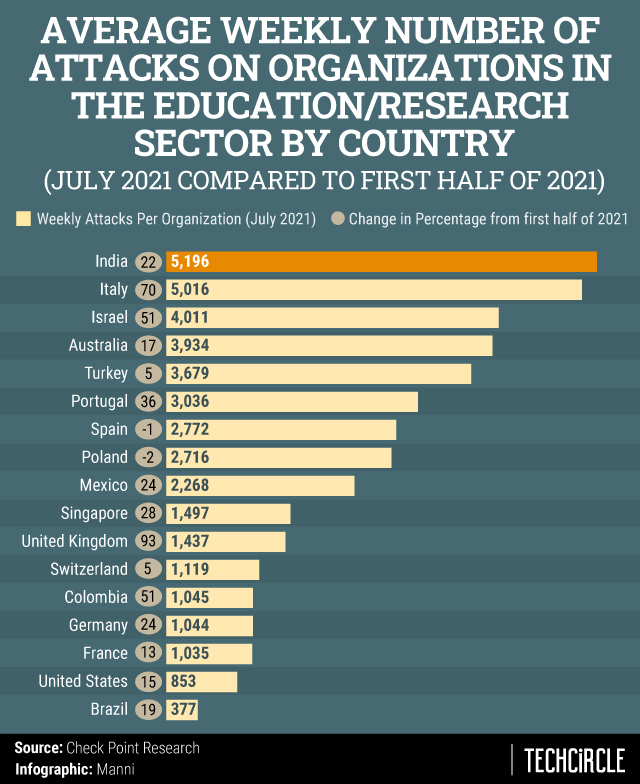
In July 2021 the education sector in India experienced the highest number of attacks averaging 5,196 attacks weekly per organization, a 22% rise from the first half of 2021. This was followed by Italy with an average of 5,016 attacks and Israel, with 4,011 attacks on a weekly basis per organization.

However, if we compare in terms of the percentage rise of attacks for July 2021, compared to the first half of 2021, Italy witnessed a 70% rise in attacks, while Israel was at 51% and the UK had a steep 93% increase in cybercrime against educational organizations (India is at 22%).
CPR also said that there has been a steady increase in the weekly number of cyberattacks per organization globally, but the education and the research sectors were impacted at a greater rate than others.

Check Point noted that in more than half of the countries, the education sector was the most targeted and it was one of the top three most attacked sectors in 94% of the organizations surveyed.
The survey is part of a continuous research by Check Point on clients that use their software globally. The current blog post includes data from 17 of the top countries impacted by the attacks.
In terms of avoiding such attacks, the company suggested to review and strengthen passwords, be aware of phishing techniques, especially in terms of suspicious emails. In terms of the IT staff, Check Point said that the attack surface can be reduced to take control of peripherals, applications and network traffic, and data can be now encrypted while in motion, at rest and in use to avoid data leakages. In terms of remediation, the Israel cybersecurity provider suggested to control damage by detecting and blocking command and control traffic, along with preventing lateral movement of malware by isolation of infected machines.

