
Lakhs of open-source projects at risk due to a 15-year-old flaw in Python module

Security researchers at cybersecurity firm Trellix have found a vulnerability in the Python Tarfile module that has been in circulation for 15 years without being fixed. The researchers believe that hundreds of thousands of open-source projects are at risk of exploitation through it.
Tarfile module is used to read and write compressed files known as tar archives. The vulnerability 'CVE-2007-4559' impacts the extract and extract all functions in the tarfile module and can allow an attacker to overwrite arbitrary files by adding the “..” sequence to filenames in a TAR archive, Kasimir Schulz, a vulnerability researcher at Trellix explained in a blog post, published on September 21.
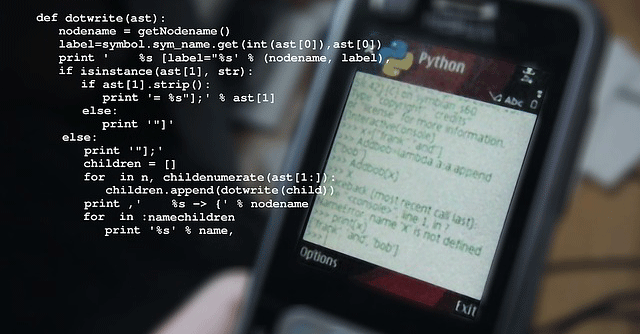
A Python module is a file that contains Python code, which can be used for performing different functions within an application.

According to Schulz, tarfile allows developers to add a filter that can be used to parse and modify a file’s metadata before it is added to the tar archive. “This enables attackers to create their exploits with as little as the 6 lines of code,” he added.
To find the number of impacted repositories, Trellix team built a Python script called Creosote, which recursively looks through directories to find the .py files and then analyses them to see if any of them have the vulnerability.
Schulz reiterated that the vulnerability is “incredibly easy” to exploit. “Due to this fact and the prevalence of the vulnerability in the wild, Python’s tarfile module has become a massive supply chain issue threatening infrastructure around the world,” warned Schulz.

According to a report in The Register, the vulnerability first surfaced in 2007 in the Python mailing list. Back then, Lars Gustable, a maintainer of the tarfile module, made some code changes that added a default true check_paths parameter and showed an error if a tar archive file path was found to be insecure. However, the fix did not address the TarFile.extract() method. Gustable then warned that the method should not be used at all.
