
Biden warns CXOs to strengthen their firms' cyber defences; Here’s how
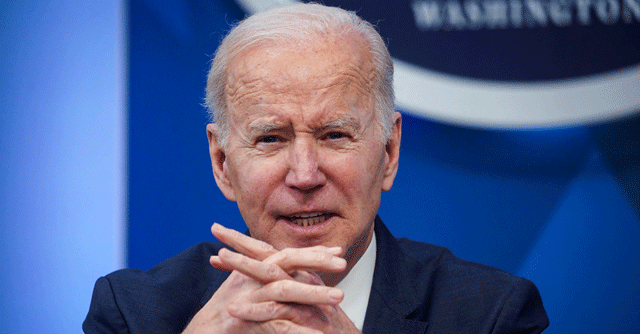

The world has braced for some sort of large-scale cyber-attack from Russia since tensions began to mount between Russia and Ukraine. Now, US President Joe Biden issued an urgent warning to business leaders, telling them to immediately strengthen their companies’ cyber defences. He said Russia is likely to use cyber-attacks as a form of retaliation against the US for its actions to counter Russia’s incursion on Ukraine.
“The magnitude of Russia’s cyber capacity is fairly consequential and it’s coming. I urge our private sector partners to harden your cyber defences immediately,” Biden said in the statement, pointing to “evolving intelligence” to suggest Russia could conduct malicious cyber activity against US companies and its critical infrastructure, including those in the, to name a few.
“It’s part of Russia’s playbook,” the President cautioned, adding everyone needed “to do their part to meet one of the defining threats of our time.”

Deputy National Security Adviser for Cyber and Emerging Technology Anne Neuberger also called for companies to secure their systems, including implementing multifactor authentication, patching systems against known vulnerabilities, backing up data, running drills and engaging with federal authorities before a cyberattack happens.
Amit Yoran, CEO of cybersecurity company Tenable and former founding director of the US-CERT program in the Department of Homeland Security said, “Critical infrastructures, largely operated by the private sector, are a significant target. The world we live in relies on these digital systems — everything from the water we drink to the electricity we use to heat our homes. We cannot afford to leave this infrastructure vulnerable.”
“The main takeaways from the President’s statement: organisations need to roll up their sleeves and secure their systems before it’s too late. We have a responsibility and duty of care, especially in turbulent times, to protect ourselves,” he said.

“To make these ongoing warnings more actionable, the Cybersecurity & Infrastructure Security Agency’s (CISA) Shields Up initiative has developed helpful resources that empower organisations to prepare for and defend against cyberattacks,” added Yoran.
Russian cyber criminals have launched several cyberattacks affecting the US and subsequently global business in recent years, including the ransomware attack on Colonial Pipeline, which led to gas shortages in May 2021, followed a few weeks later by an attack on the meat processor JBS.
Russia also carried out significant cyberattacks against Ukraine in years past, including the devastating NotPetya attack in 2017 that spread far and wide and caused more than $10 billion in damage to IT systems around the world.

Since Russia’s invasion of Ukraine, the former imposed domestic online censorship by blocking Facebook, Instagram and limited Twitter usage. Soon after major tech companies — including Apple, Microsoft, Oracle, Google, Intel, AMD, HP Inc., HPE, Dell and more — are complying with strict and historic sanctions against Russia. Multinational corporations are joining in the boycott effort as well.
According to a White House fact sheet, companies should take the following actions:
- Mandate the use of multi-factor authentication on your systems to make it harder for attackers to get onto your system;
- Deploy modern security tools on your computers and devices to continuously look for and mitigate threats;
- Check with your cybersecurity professionals to make sure that your systems are patched and protected against all known vulnerabilities, and change passwords across your networks so that previously stolen credentials are useless to malicious actors;
- Back up your data and ensure you have offline backups beyond the reach of malicious actors;
- Run exercises and drill your emergency plans so that you are prepared to respond quickly to minimise the impact of any attack; Encryption
- Encrypt your data so it cannot be used if it is stolen.
- Educate your employees to common tactics that attackers will use over email or through websites, and encourage them to report if their computers or phones have shown unusual behaviour, such as unusual crashes or operating very slowly.
- Engage proactively with your local FBI field office or CISA Regional Office to establish relationships in advance of any cyber incidents.
- Encourage your IT and Security leadership to visit the websites of CISA and the FBI where they will find technical information and other useful resources.
Steven Hope, CEO of UK-based password security management firm, Authlogics, has stressed on the necessity to manage passwords in the face of adversity. “Weak passwords make it easy for Russian state-sponsored hackers to access multi-factor authentication (MFA) ‘protected’ accounts.”

“Now, following a cybersecurity advisory from the Federal Bureau of Investigation and Cybersecurity and Infrastructure Security Agency, we have all been given a stark reminder of the necessity to manage passwords,” he said.
Improving Long Term Cyber Security
To attain long-term cybersecurity for the economy, the White House further recommended technology and software companies to build security into your products from the ground up to protect both your intellectual property and your customers’ privacy.”

Other recommendations include, develop software only on a system that is highly secure and accessible only to those actually working on a particular project. This will make it much harder for an intruder to jump from system to system and compromise a product or steal your intellectual property.
On the whole, companies need to protect themselves against potential Russian cyberattacks immediately, as experts agreed those that have not strengthened their cyber defences are at a significantly greater risk of compromise.
